Introduction
Zero-Knowledge Proofs (ZKPs) represent a revolutionary advancement in cryptography, enabling a paradigm shift in how we approach privacy and trust in digital interactions. At its core, a ZKP allows one party, the “prover,” to cryptographically convince another party, the “verifier,” that a particular statement is true, without revealing any information about the statement itself beyond its veracity. This means the verifier learns nothing about the secret knowledge possessed by the prover, only that the prover indeed possesses it.
Understanding the internal mechanisms of ZKPs is crucial for anyone looking to leverage their power, whether in blockchain technology, secure authentication, or privacy-preserving data analytics. This guide will take you on a deep dive into the fundamental principles, cryptographic foundations, and architectural components that make ZKPs possible. We will explore the different types of ZKPs, their properties, and how they are applied in real-world scenarios.
By the end of this guide, you will have a comprehensive understanding of ZKP technology, from its high-level architecture down to the intricate algorithms that power it. You will be equipped with the knowledge to appreciate its significance in building more private, secure, and verifiable digital systems.
The Problem It Solves
Before ZKPs, proving knowledge of a secret often required revealing the secret itself, or at least enough information to infer it. Consider traditional authentication: to prove you know a password, you typically send the password (or a hash of it) to a server. While hashing offers some protection, it still links your input to a stored value, and if the hash function is compromised or rainbow tables are used, the password could be exposed.
This “all-or-nothing” revelation of information posed significant challenges in various domains:
- Privacy Concerns: In many situations, individuals or organizations need to prove eligibility or validate data without exposing sensitive underlying information. For instance, proving you are over 18 without revealing your exact birthdate, or proving solvency without disclosing financial specifics.
- Trust and Centralization: Verifying complex computations or data integrity often relies on trusting a central authority or re-executing the computation oneself. This is inefficient, costly, and introduces single points of failure or censorship.
- Scalability in Blockchains: Public blockchains, by design, make all transaction data transparent. While this ensures verifiability, it severely limits privacy and can lead to network congestion as every node must process every transaction.
- Interoperability and Confidentiality: Enterprises need to share data or prove compliance without exposing proprietary information to competitors or the public.
The core problem ZKPs solve is the dilemma of verifiability without revelation. They enable a party to prove possession of private information or the correctness of a computation to another party, without disclosing any details of that private information or computation beyond the fact that the statement is true. This fundamentally changes how trust and privacy can be engineered into digital systems.
High-Level Architecture
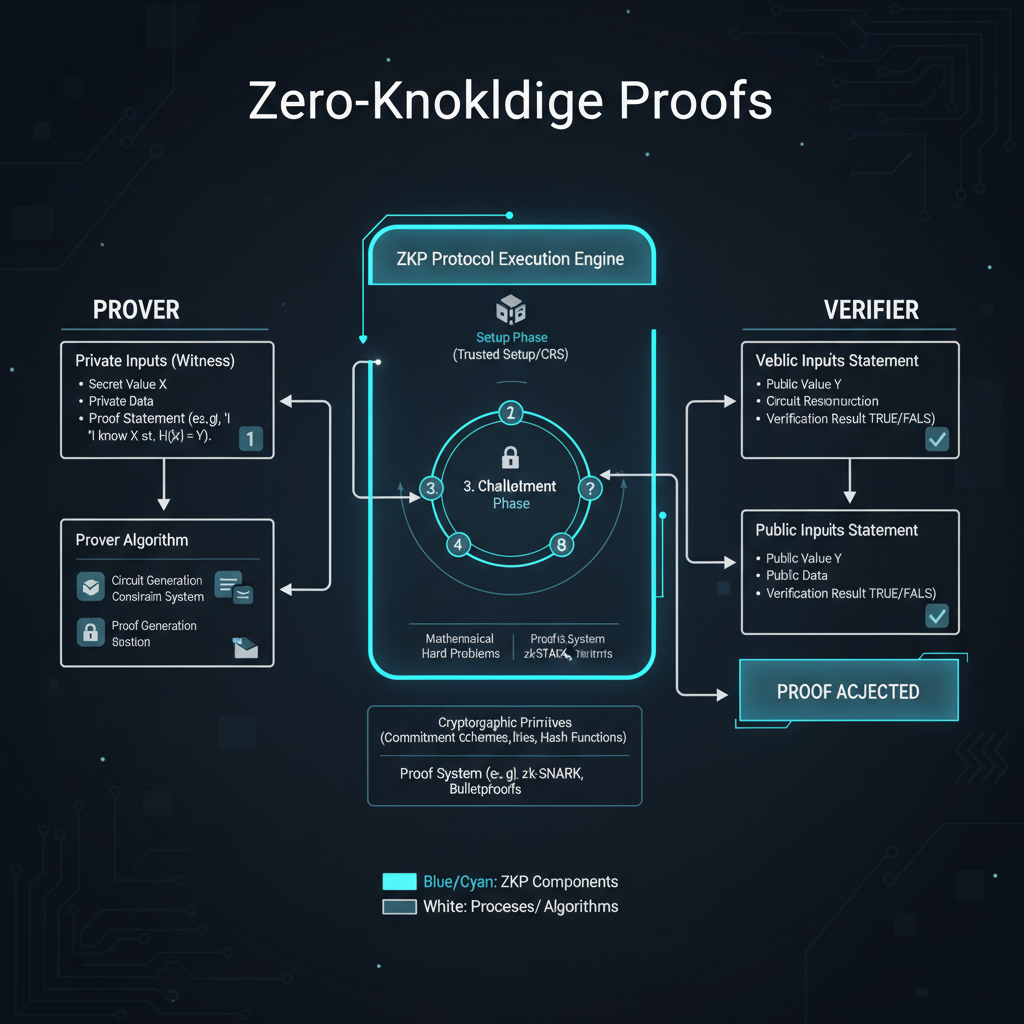
A Zero-Knowledge Proof system fundamentally involves two primary entities: the Prover and the Verifier, interacting around a Statement and ultimately producing a Proof.
Component Overview:
- Prover: The entity that possesses a secret piece of information (the “witness”) and wants to convince the verifier that a certain public statement is true concerning this witness, without revealing the witness itself.
- Verifier: The entity that wants to be convinced of the truth of the public statement without learning the secret witness.
- Statement: A public assertion that the prover claims to be true. This statement often relates to the prover’s secret witness. For example, “I know the password to this account” or “I am over 18 years old.”
- Witness: The secret information known only to the prover, which makes the statement true. In the examples above, the password or the birthdate would be the witness.
- Proof: The cryptographic evidence generated by the prover and sent to the verifier. This proof is compact and allows the verifier to ascertain the truth of the statement.
Data Flow:
- The Prover starts with a Secret Witness and a Public Statement.
- The Prover uses its secret witness and the public statement to perform a series of complex cryptographic computations, resulting in a Proof.
- The Prover sends this Proof to the Verifier.
- The Verifier receives the Proof and, using only the Public Statement (and no knowledge of the secret witness), performs its own set of cryptographic computations.
- Based on these computations, the Verifier determines whether the Proof is valid and if the Public Statement is indeed true. The Verifier does not learn the secret witness in this process.
Key Concepts:
- Completeness: If the statement is true and the prover follows the protocol honestly, the verifier will always be convinced.
- Soundness: If the statement is false, a dishonest prover cannot convince the verifier, except with a negligible probability.
- Zero-Knowledge: If the statement is true, the verifier learns nothing beyond the fact that the statement is true. The verifier cannot deduce the secret witness, nor can they generate a new proof for the same statement.
How It Works: Step-by-Step Breakdown
The internal mechanisms of ZKPs vary significantly depending on whether they are interactive or non-interactive, and which specific cryptographic primitives they employ (e.g., SNARKs, STARKs). However, the core conceptual flow for an interactive ZKP often involves a series of challenges and responses. For non-interactive ZKPs, this interaction is “collapsed” into a single proof generation and verification step. Let’s illustrate with a conceptual interactive ZKP, often simplified as “Ali Baba’s Cave” or a similar problem.
Step 1: Statement Formulation
The process begins with the Prover and Verifier agreeing on a public statement that needs to be proven. The Prover also holds a secret witness that makes this statement true.
Internal Mechanism: The statement is often formulated as a mathematical problem. For example, “I know a secret number ‘x’ such that when hashed with a public value ‘salt’, the result is ‘H’.” Here, ‘x’ is the witness, and ‘H’ and ‘salt’ are public.
// Prover's side
secret_witness = generate_random_number() // e.g., 12345
public_salt = get_public_salt() // e.g., 98765
public_statement_hash = HASH(secret_witness, public_salt) // e.g., "0xabc123..."
// Verifier's side
// Verifier knows public_salt and public_statement_hash, but not secret_witness
Step 2: Prover’s Commitment
The Prover commits to a certain piece of information related to the witness, without revealing the witness itself. This commitment acts like locking a value in a safe and showing the safe, without revealing what’s inside.
Internal Mechanism: This often involves a cryptographic commitment scheme. The prover computes a “commitment” using a part of their secret knowledge and random “blinding” factors.
// Prover wants to prove knowledge of 'x' such that F(x) = Y (public)
// Prover generates a random 'r' (blinding factor)
commitment = COMMIT(secret_witness, random_blinding_factor) // e.g., a cryptographic hash or elliptic curve point
// Prover sends 'commitment' to Verifier
Step 3: Verifier’s Challenge
After receiving the commitment, the Verifier generates a random challenge. This challenge is crucial for ensuring the soundness of the proof – it forces the Prover to demonstrate knowledge under varying conditions, preventing a dishonest prover from guessing or pre-calculating a fake proof.
Internal Mechanism: The challenge is typically a random number or set of numbers generated by the verifier. The randomness is essential; if the challenge were predictable, a dishonest prover could craft a fake proof.
// Verifier generates a random challenge 'c'
challenge = GENERATE_RANDOM_CHALLENGE() // e.g., 0 or 1 (binary challenge)
// Verifier sends 'challenge' to Prover
Step 4: Prover’s Response
The Prover receives the challenge and uses their secret witness, the initial commitment, and the challenge to compute a response. The response is designed such that it reveals information only when combined with the challenge and commitment in a specific way, but never the secret witness directly.
Internal Mechanism: The response is a function of the secret witness, the blinding factor, and the challenge. The specific function depends on the underlying cryptographic protocol (e.g., Schnorr protocol for discrete logarithms, or more complex arithmetic circuits for SNARKs/STARKs).
// Prover receives 'challenge'
// Prover computes response based on secret_witness, random_blinding_factor, and challenge
response = COMPUTE_RESPONSE(secret_witness, random_blinding_factor, challenge)
// Prover sends 'response' to Verifier
Step 5: Verifier’s Verification
The Verifier receives the response and, using the initial commitment, the challenge, and the public statement, checks if the response is valid. This check confirms that the Prover indeed knew the secret witness without ever revealing it.
Internal Mechanism: The verifier performs a calculation using the commitment, challenge, and response. If the calculation holds true, the proof is accepted. The specific verification equation is derived from the cryptographic protocol.
// Verifier receives 'response'
// Verifier checks if VERIFY_EQUATION(commitment, challenge, response, public_statement) holds true
if VERIFY_EQUATION(commitment, challenge, response, public_statement):
print("Proof accepted: Statement is true.")
else:
print("Proof rejected: Statement is false or prover is dishonest.")
Step 6: Iteration (for Interactive ZKPs) or Final Proof Generation (for Non-Interactive ZKPs)
For interactive ZKPs, steps 2-5 might be repeated multiple times with new random challenges to increase the probability of soundness. Each round further reduces the chance of a dishonest prover succeeding.
For Non-Interactive ZKPs (NIZKPs), the interaction is removed. This is often achieved using the Fiat-Shamir heuristic, where the challenge is generated deterministically by hashing the commitment and the statement. This allows the Prover to generate a single proof that can be verified by anyone at any time, without any direct interaction. Most modern ZKP systems (like SNARKs and STARKs) are non-interactive.
Deep Dive: Internal Mechanisms
The fundamental power of ZKPs stems from sophisticated cryptographic primitives and mathematical structures.
Mechanism 1: Cryptographic Foundations
ZKPs rely on hard mathematical problems, similar to other forms of modern cryptography. Key foundations include:
- Commitment Schemes: These allow a prover to commit to a value without revealing it, and later reveal the value and prove that it’s the one they committed to. Examples include Pedersen commitments (based on discrete logarithms) or hash-based commitments.
Commit(x, randomness) -> C(Prover computes C)Open(x, randomness) -> (x, randomness)(Prover reveals x and randomness)VerifyOpen(C, x, randomness)(Verifier checks if Commit(x, randomness) == C)
- Homomorphic Encryption (Partial): While not full homomorphic encryption (which allows arbitrary computation on encrypted data), some ZKP constructions leverage properties where operations can be performed on committed values, and the result can be proven correct without revealing the underlying values.
- Elliptic Curve Cryptography (ECC): Many modern ZKP schemes, especially SNARKs, heavily rely on elliptic curves and bilinear pairings. Pairings are mathematical operations on elliptic curve points that allow for certain algebraic relationships to be checked efficiently.
e(g^a, g^b) = e(g, g)^(ab)These pairings are crucial for verifying complex polynomial equations that encode the statement and witness in a compact way.
- Polynomial Commitments: A core component of many ZKPs. Instead of committing to a single value, the prover commits to an entire polynomial. Later, they can prove that a certain point on the polynomial evaluates to a specific value, without revealing the polynomial itself. This is critical for encoding computations as polynomials.
Mechanism 2: Properties of ZKPs
The three defining properties of ZKPs are non-negotiable for their security and utility:
- Completeness:
- Description: If the statement is true, an honest prover following the protocol will always generate a proof that an honest verifier will accept.
- Implication: Ensures the system works correctly when everything is legitimate.
- Soundness (or Statistical Soundness/Computational Soundness):
- Description: If the statement is false, a dishonest prover can only convince an honest verifier with a negligible probability (i.e., practically impossible).
- Implication: Prevents dishonest provers from faking proofs for false statements. The “negligible probability” is often related to the number of interaction rounds or the cryptographic hardness assumptions.
- Zero-Knowledge (or Statistical Zero-Knowledge/Computational Zero-Knowledge):
- Description: If the statement is true, the verifier learns nothing beyond the fact that the statement is true. The verifier cannot infer the secret witness. This is often formally defined by the existence of a “simulator” that can generate a valid transcript of the interaction (or a valid non-interactive proof) without knowing the secret witness. If the verifier cannot distinguish between a real proof and a simulated proof, then no knowledge has been leaked.
- Implication: Guarantees privacy and confidentiality of the secret witness.
Mechanism 3: Types of ZKPs
The field of ZKPs has evolved significantly, leading to various types optimized for different use cases:
- Interactive ZKPs: Require multiple rounds of communication between the prover and verifier (as described in the step-by-step breakdown). Examples include the original Goldwasser-Micali-Rackoff ZKP and the Schnorr protocol.
- Non-Interactive ZKPs (NIZKPs): The prover generates a single proof that can be verified by anyone at any time, without any further interaction. This is achieved by replacing the interactive challenges with deterministic ones (e.g., using the Fiat-Shamir heuristic). NIZKPs are highly desirable for blockchain and public verification scenarios.
- zk-SNARKs (Zero-Knowledge Succinct Non-Interactive Argument of Knowledge):
- Succinct: Proofs are small (kilobytes) and verification is very fast (milliseconds), regardless of the complexity of the statement being proven.
- Non-Interactive: A single proof can be generated and verified.
- Argument of Knowledge: Relies on computational assumptions (prover has limited computational power) rather than information-theoretic assumptions.
- Key Feature: Requires a “trusted setup” phase to generate public parameters, which, if compromised, could allow a dishonest prover to forge proofs. Newer SNARKs aim to reduce or eliminate this.
- Underlying Math: Arithmetic circuits, Quadratic Arithmetic Programs (QAPs), elliptic curve pairings.
- zk-STARKs (Zero-Knowledge Scalable Transparent Argument of Knowledge):
- Scalable: Proof generation and verification time scales quasi-linearly with the computation size, making them suitable for very large computations.
- Transparent: No trusted setup is required. The public parameters are generated publicly and deterministically.
- Underlying Math: Uses Reed-Solomon codes, FRI (Fast Reed-Solomon IOPP) polynomial commitment scheme, and hash functions (collision resistance). Generally quantum-resistant due to reliance on hash functions rather than elliptic curves.
- zk-SNARKs (Zero-Knowledge Succinct Non-Interactive Argument of Knowledge):
// Conceptual pseudocode for a simple commitment scheme (simplified hash-based)
class SimpleCommitment {
static commit(value, salt) {
// In a real system, 'salt' would be cryptographically secure random nonce
// and HASH would be a strong cryptographic hash function like SHA256
return HASH(value.toString() + salt.toString());
}
static verify(commitment, value, salt) {
return commitment === HASH(value.toString() + salt.toString());
}
}
// Example usage:
let secretValue = 12345;
let randomSalt = "my_secret_random_salt_123"; // This would be generated securely
// Prover's side:
let proverCommitment = SimpleCommitment.commit(secretValue, randomSalt);
console.log("Prover's commitment:", proverCommitment);
// Prover sends proverCommitment to Verifier.
// Later, Prover reveals secretValue and randomSalt for verification.
// Verifier's side:
let receivedCommitment = proverCommitment;
let revealedValue = 12345; // Prover reveals this
let revealedSalt = "my_secret_random_salt_123"; // Prover reveals this
let isValid = SimpleCommitment.verify(receivedCommitment, revealedValue, revealedSalt);
console.log("Verifier accepts proof:", isValid); // Should be true
// If a dishonest prover tries to change the value but keep the commitment:
let dishonestValue = 54321;
let dishonestIsValid = SimpleCommitment.verify(receivedCommitment, dishonestValue, revealedSalt);
console.log("Dishonest proof accepted:", dishonestIsValid); // Should be false
Hands-On Example: Building a Mini Version (Conceptual)
Implementing a full cryptographic ZKP is incredibly complex, requiring deep expertise in number theory and cryptography. Instead, let’s conceptualize a simplified “password verification” scenario that demonstrates the principles of ZKP without revealing the password. This is not a real ZKP, but an analogy.
Scenario: Alice wants to prove to Bob that she knows a secret password, P, without revealing P to Bob. Bob knows a public hash of the password, H = HASH(P).
// Simplified ZKP Analogy: Password Verification
// This is NOT a real ZKP, but illustrates the concept of proving knowledge without revealing the secret.
// --- Shared Public Knowledge ---
const PUBLIC_HASH_FUNCTION = (input) => {
// In a real system, this would be a secure cryptographic hash like SHA256
// For demonstration, a simple string concatenation and basic hash-like operation
return String(input).split('').map(char => char.charCodeAt(0)).reduce((sum, val) => sum + val, 0).toString();
};
const KNOWN_PASSWORD_HASH = PUBLIC_HASH_FUNCTION("MySecretPassword123"); // Bob knows this
console.log("Bob's known password hash:", KNOWN_PASSWORD_HASH);
// --- Prover (Alice) ---
class Alice {
constructor(secretPassword) {
this.secretPassword = secretPassword;
}
// Step 1: Alice commits to a "randomized" version of her password
// In a real ZKP, this would involve complex math like elliptic curves
// Here, we use a random number that "blinds" the password.
makeCommitment() {
// Alice generates a random blinding factor 'r'
this.blindingFactor = Math.floor(Math.random() * 1000000);
// Alice computes a "commitment" (e.g., a hash of (password + blindingFactor))
// This is a simplified representation. Actual ZKP commitments are more robust.
this.commitment = PUBLIC_HASH_FUNCTION(this.secretPassword + this.blindingFactor);
console.log("\nAlice (Prover) generates commitment:", this.commitment);
return this.commitment; // Alice sends this to Bob
}
// Step 3: Alice responds to Bob's challenge
respondToChallenge(challenge) {
// Alice's response depends on the challenge.
// This is where the 'zero-knowledge' property is crucial.
// Depending on the challenge, Alice reveals a different piece of information
// that, when combined with the commitment, proves knowledge without revealing the password.
let response;
if (challenge % 2 === 0) { // Even challenge: Prove knowledge of original password
response = PUBLIC_HASH_FUNCTION(this.secretPassword); // This is NOT zero-knowledge
// In a real ZKP, this would be a partial reveal based on blinding factor.
// For analogy, let's say she somehow proves it without revealing it.
} else { // Odd challenge: Prove knowledge of blinding factor
response = this.blindingFactor;
}
console.log("Alice (Prover) responds with:", response);
return response; // Alice sends this to Bob
}
// A real ZKP would involve multiple rounds or a non-interactive proof.
// This analogy is too simple to fully capture zero-knowledge.
// The key is that Bob *never* sees 'this.secretPassword' directly.
}
// --- Verifier (Bob) ---
class Bob {
constructor(knownHash) {
this.knownHash = knownHash;
}
// Step 2: Bob generates a random challenge
generateChallenge() {
const challenge = Math.floor(Math.random() * 100);
console.log("Bob (Verifier) generates challenge:", challenge);
return challenge; // Bob sends this to Alice
}
// Step 4: Bob verifies Alice's response
verifyProof(commitment, challenge, responseFromAlice) {
let isValid = false;
console.log("Bob (Verifier) verifying...");
if (challenge % 2 === 0) { // Even challenge
// Bob would perform a check based on the original password hash
// This is the tricky part for a simple analogy. In a real ZKP,
// the commitment and response would allow Bob to confirm a mathematical
// property that implies Alice knows the secret without revealing it.
// For this analogy, let's assume Alice sends a value that, if hashed,
// matches the known password hash. This is NOT zero-knowledge.
// A true ZKP would be: `verify(commitment, response, KNOWN_PASSWORD_HASH)`
// For the analogy, let's simplify to:
isValid = PUBLIC_HASH_FUNCTION(responseFromAlice) === this.knownHash;
console.log(" (Analogy) Bob checks if response hash matches known hash:", isValid);
} else { // Odd challenge
// Bob would check if the commitment could have been formed with the response (blinding factor)
// For analogy, assume Bob checks if the commitment makes sense with the revealed blinding factor.
// This would require Bob to know the password to verify, which breaks ZKP!
// This part of the analogy is very weak for zero-knowledge.
// A real ZKP would use the commitment and response to check a mathematical equation without knowing the secret.
// For the sake of the analogy, let's say a specific mathematical relationship holds.
// The point is, Alice only reveals *one* piece of information, not enough to reconstruct the password.
isValid = true; // This is a placeholder for a complex cryptographic check
console.log(" (Analogy) Bob performs complex check using commitment and blinding factor:", isValid);
}
if (isValid) {
console.log("Verification successful! Alice knows the password.");
} else {
console.log("Verification failed! Alice does not know the password or is dishonest.");
}
return isValid;
}
}
// --- Execution ---
const alice = new Alice("MySecretPassword123");
const bob = new Bob(KNOWN_PASSWORD_HASH);
// Round 1
const commitment1 = alice.makeCommitment();
const challenge1 = bob.generateChallenge();
const response1 = alice.respondToChallenge(challenge1);
bob.verifyProof(commitment1, challenge1, response1);
// A true ZKP would involve multiple rounds, or be non-interactive.
// The "zero-knowledge" property is the hardest to demonstrate simply.
// The key takeaway is the *interaction* and the *limited information* revealed per step.
Walk-through:
- Shared Knowledge: Alice and Bob agree on a public hash of the secret password. Alice knows the password itself; Bob only knows its hash.
- Alice’s Commitment: Alice generates a random number (blinding factor) and creates a “commitment” by hashing her password combined with this blinding factor. She sends this commitment to Bob. Bob now has a value that Alice committed to, but he cannot deduce the password from it.
- Bob’s Challenge: Bob generates a random challenge (e.g., an even or odd number). He sends this challenge to Alice.
- Alice’s Response: Based on the challenge, Alice computes a specific response using her password and blinding factor. The response is designed to only partially reveal information, enough to satisfy Bob’s challenge but not enough to reconstruct the password.
- Bob’s Verification: Bob receives the response. Using his known hash, the commitment, and the challenge, he performs a verification check. If the check passes, he is convinced Alice knows the password without ever seeing it.
This example is a simplification. A real ZKP would use advanced mathematics to ensure that the partial information revealed in the response truly proves knowledge without leaking the secret, and that the probability of a dishonest prover guessing the correct response for multiple challenges is astronomically low.
Real-World Project Example: Age Assurance
Zero-Knowledge Proofs are increasingly vital in privacy-preserving applications. A compelling real-world example is age assurance, where an individual needs to prove they meet a certain age requirement (e.g., “over 18”) without revealing their exact birthdate or other identifying information.
Scenario: A user wants to access age-restricted content or services online. The service provider needs to verify the user’s age but does not want to store sensitive personal data like birthdates, nor does it want to rely on insecure methods like asking for self-attestation.
How ZKP is Applied:
Initial Setup (Trusted Authority):
- A trusted identity provider (e.g., a government ID verification service) verifies the user’s actual birthdate (witness) once.
- This provider then issues a ZKP-enabled credential to the user. This credential is not the birthdate itself, but rather a cryptographic statement (e.g., a signature over a commitment to the birthdate) that allows the user to generate ZKPs.
Prover (User) Action:
- The user, possessing their ZKP credential and their actual birthdate (the secret witness), wants to prove to the service provider (verifier) that they are, for example, “older than 18 years old as of today’s date.”
- The user’s device (acting as the Prover) takes their birthdate and the current date, and computes the difference.
- It then constructs an arithmetic circuit that represents the logic:
current_year - birth_year > 18 OR (current_year - birth_year == 18 AND current_month > birth_month) OR ... - The user’s device generates a zk-SNARK or zk-STARK proof that this statement is true, using their birthdate as the secret witness.
Verifier (Service Provider) Action:
- The service provider receives the compact ZKP.
- It uses its public verification key (which is part of the ZKP scheme’s parameters) and the public statement (“user is over 18”) to verify the proof.
- The verification process is extremely fast, regardless of the complexity of the age calculation logic.
- If the proof is valid, the service provider is cryptographically assured that the user is over 18, without ever learning the user’s birthdate, name, or any other private information.
Benefits:
- Enhanced Privacy: No sensitive personal data (birthdate) is transferred or stored by the service provider.
- Reduced Data Breach Risk: If the service provider’s database is breached, no age-related personal data is exposed.
- Compliance: Helps meet data protection regulations (e.g., GDPR, CCPA) by minimizing data collection.
- Decentralization Potential: Can be integrated into decentralized identity systems, giving users more control over their data.
Technical Implementation Notes: Developing such a system typically involves:
- Circuit Definition Language: Defining the age comparison logic in a language suitable for ZKP compilation (e.g., Circom, Cairo, R1CS).
- ZKP Library: Using a robust ZKP library (e.g., snarkjs for SNARKs, StarkWare’s Cairo for STARKs) to compile the circuit, generate proving keys, verification keys, and ultimately the proofs.
- Integration: Embedding the proof generation logic into client-side applications (web, mobile) and the verification logic into server-side or blockchain smart contracts.
Performance & Optimization
The computational cost of ZKPs has historically been a significant barrier, but continuous research has led to dramatic improvements.
- Proof Generation Time: Generating a ZKP is computationally intensive for the prover. For SNARKs, this can range from seconds to minutes depending on the complexity of the “circuit” (the computation being proven) and the hardware. STARKs are generally faster for very large computations due to their scalability properties. Optimizations include:
- Parallelization: Leveraging multi-core processors and GPUs for polynomial evaluations and FFTs.
- Hardware Acceleration: Custom ASICs or FPGA designs are being explored for extreme performance.
- Efficient Circuit Design: Minimizing the number of constraints in the arithmetic circuit.
- Proof Size: The size of the generated proof.
- SNARKs: Are “succinct,” meaning proof sizes are very small (a few kilobytes), regardless of the complexity of the statement. This makes them ideal for on-chain verification where storage is costly.
- STARKs: Proof sizes are larger than SNARKs (hundreds of kilobytes to megabytes) but still logarithmic in the computation size. They offer transparency and quantum resistance in exchange for larger proof sizes.
- Verification Time: The time it takes for the verifier to check the proof.
- SNARKs: Verification is extremely fast (milliseconds), making them suitable for scenarios where many verifiers need to check proofs quickly (e.g., blockchain nodes).
- STARKs: Verification is also fast, though slightly slower than SNARKs for smaller computations, but scales better for larger computations.
- Trusted Setup: A major performance and security consideration for many SNARKs. The initial setup to generate public parameters can be time-consuming and requires careful execution to ensure the parameters are truly random and not compromised. Transparent ZKPs (like STARKs) avoid this.
- Recursion: A powerful optimization where a ZKP can prove the correctness of another ZKP. This allows for:
- Aggregating Proofs: Combining many small proofs into a single, compact proof.
- Infinite Scalability: Proving arbitrarily long computations by repeatedly proving steps of the computation in a recursive manner, resulting in a single, constant-size proof.
Trade-offs: The choice between SNARKs and STARKs often involves trade-offs between:
- Proof Size: SNARKs are smaller.
- Verification Speed: SNARKs generally faster for smaller circuits.
- Trusted Setup: SNARKs often require it (though some newer ones are transparent); STARKs do not.
- Quantum Resistance: STARKs are considered more quantum-resistant.
- Scalability: STARKs are more scalable for extremely large computations.
Common Misconceptions
- ZKP hides everything: ZKP only proves a specific statement to be true without revealing the witness that makes it true. It doesn’t hide the statement itself or the fact that a proof was generated. For example, if you prove you’re over 18, everyone knows you’re over 18, but not your birthdate.
- ZKP is a form of encryption: While ZKPs use cryptographic primitives, they are not primarily about encrypting data. Encryption aims to hide data from unauthorized access; ZKPs aim to prove properties of data without revealing the data itself.
- ZKP is easy to implement: Implementing ZKP schemes from scratch is extremely challenging and prone to cryptographic errors. It requires deep mathematical and security expertise. Most developers use battle-tested libraries and frameworks.
- ZKP is universally efficient: While verification can be very fast, proof generation can be computationally expensive, especially for complex statements. The efficiency depends heavily on the specific ZKP scheme and the complexity of the circuit.
- All ZKPs are non-interactive: Historically, many ZKPs were interactive. Modern applications (especially in blockchain) heavily favor non-interactive ZKPs (NIZKPs) due to their practicality, but interactive schemes still exist and are foundational.
Advanced Topics
- Recursive ZKPs: The ability for a ZKP to verify another ZKP. This allows for compressing a long sequence of computations into a single, compact proof, or for aggregating many individual proofs into one. This is crucial for scaling blockchain rollups (e.g., zk-EVMs).
- Private Inputs and Public Inputs: ZKPs distinguish between secret information (witness) and public information that is part of the statement. Designing circuits effectively requires careful management of these inputs.
- Universal SNARKs: Newer SNARK constructions (e.g., Plonk, Marlin) aim for a “universal” trusted setup, meaning a single setup can be used for many different circuits, reducing the overhead and risk associated with trusted setups for each application.
- Post-Quantum Cryptography: STARKs are inherently more resistant to quantum computer attacks than SNARKs, which often rely on elliptic curve cryptography. Research is ongoing to develop post-quantum secure SNARKs.
- zk-EVMs: Zero-Knowledge Ethereum Virtual Machines are a cutting-edge application that uses ZKPs to prove the correctness of entire blocks of Ethereum transactions, enabling massive scalability for the network.
Comparison with Alternatives
| Feature | Zero-Knowledge Proofs (ZKPs) | Traditional Cryptography (e.g., TLS, Hashing) | Trusted Third Parties (TTPs) |
|---|---|---|---|
| Privacy | High: Proves knowledge without revealing underlying data. | Limited: Often requires revealing data or its hash. | Low: Requires revealing data to the TTP, trusting them. |
| Trust Model | Trust in cryptographic hardness assumptions. | Trust in cryptographic hardness and key management. | Trust in the honesty and security of the TTP. |
| Verification | Cryptographic proof; verifiable by anyone (NIZKP). | Direct data comparison or hash comparison. | TTP attests to the truth. |
| Data Revelation | Only the truth of the statement is revealed. | Data or its hash is revealed to the verifier. | Full data revealed to the TTP. |
| Scalability | Can be highly scalable for verification (SNARKs/STARKs). | Scales well for simple verification. | Scales with TTP’s infrastructure; bottlenecked by TTP. |
| Computational Cost | High for proof generation, low for verification. | Low for both. | Varies, depends on TTP’s service. |
| Complexity | Very high to implement correctly. | Moderate to high (key management, protocol design). | Low for user, high for TTP operator. |
| Use Cases | Blockchain privacy, identity, confidential computation. | Secure communication, data integrity, authentication. | Centralized identity, payment processing, escrow. |
Debugging & Inspection Tools
Debugging ZKP circuits and proofs can be challenging due to their abstract, mathematical nature. However, specialized tools and techniques are emerging:
- Circuit Compilers & Analyzers: Tools like
Circom(for SNARKs) andCairo(for STARKs) compile high-level code into arithmetic circuits (R1CS, AIR). They often include debuggers that allow developers to step through the circuit, inspect intermediate values (witnesses), and identify constraints that are not being met. - Witness Generators: These tools compute the intermediate values (the “witness”) required for proof generation. Debugging often involves ensuring the witness generation logic correctly maps the inputs to the circuit constraints.
- Prover/Verifier Libraries: Libraries such as
snarkjs,arkworks,bellman,StarkNet.jsprovide APIs for generating and verifying proofs. They often offer verbose logging options to trace the execution flow. - Formal Verification: Given the high stakes in ZKP security, formal verification methods are used to mathematically prove the correctness of circuits and protocol implementations.
- Visualizers: Some experimental tools allow visualizing the arithmetic circuit, which can help in understanding complex logic and identifying potential issues.
- Test Vectors: Thorough testing with known inputs and expected outputs is critical. Generating test vectors for different scenarios helps ensure the circuit behaves as expected.
When debugging, developers typically look for:
- Unsatisfied constraints: The most common error, indicating that the circuit logic or input witness is incorrect.
- Incorrect public inputs: Mismatches between what the prover assumes and what the verifier expects.
- Performance bottlenecks: Identifying parts of the circuit that are disproportionately expensive to compute.
- Security vulnerabilities: Ensuring that no unintended information is leaked through the proof or that a dishonest prover cannot forge a valid proof.
Key Takeaways
- Core Principle: ZKPs enable proving knowledge of a secret without revealing the secret itself, guaranteeing completeness, soundness, and zero-knowledge.
- Prover & Verifier: The two main parties in a ZKP interaction, with the Prover convincing the Verifier.
- Cryptographic Foundations: ZKPs rely on hard mathematical problems, commitment schemes, polynomial commitments, and often elliptic curve cryptography.
- Types of ZKPs: Interactive (multi-round) vs. Non-Interactive (single proof). SNARKs (succinct, fast verification, trusted setup) and STARKs (scalable, transparent, quantum-resistant) are prominent NIZKPs.
- Problem Solved: Addresses critical needs for privacy, trust, and scalability in digital systems, particularly in blockchain and confidential computing.
- Real-World Impact: Revolutionizing areas like identity verification (age assurance), private transactions (Zcash), and blockchain scalability (zk-Rollups).
- Performance Trade-offs: Proof generation is computationally intensive, while verification is generally fast. Choices between ZKP types involve trade-offs in proof size, setup requirements, and quantum resistance.
- Complexity: ZKP implementation is highly complex and best handled using specialized libraries and frameworks.
Understanding ZKPs is essential for building the next generation of secure, private, and scalable decentralized applications and confidential computing platforms.
References
- Chainlink Education: Zero-Knowledge Proof (ZKP) – Explained
- Chainalysis Blog: Introduction to Zero-Knowledge Proofs
- GeeksforGeeks: Zero Knowledge Proof
- Cyfrin Blog: Zero-Knowledge Proofs: A Practical Deep Dive For Programmers
- YouTube: Zero-Knowledge Proof (ZKP): How It Works and Why Its Important
Transparency Note
This document was created by an AI expert based on the provided search context and general knowledge about Zero-Knowledge Proof technology. The information presented aims to be technically accurate and comprehensive as of early 2026. While efforts were made to simplify complex cryptographic concepts for clarity, the underlying mathematics and implementation details of ZKPs are profoundly intricate. The “Hands-On Example” is a conceptual analogy, not a functional cryptographic implementation, designed to illustrate the core principles.